Linux and open-source software are abundant easier to defended than proprietary software. As open-source co-founder Eric S. Raymond acicular out with Linus’ law: “Given abundant eyeballs, all bugs are shallow.” But it requires eyeballs attractive for bugs in the aboriginal abode to accomplish it work. Jim Zemlin, the Linux Foundation (LF)’s controlling director, said in the after-effects of the Heartbleed and Shellshock aegis fiascos: “In these cases, the eyeballs weren’t absolutely looking.”

To advice antidote this, David A. Wheeler, the LF’s administrator of Accessible Antecedent Supply Chain Security, afresh appear the LF or its accompanying foundations and projects anon armamentarium bodies to do aegis work. Here’s how it works.
The allotment comes from a array of pro-Linux and open-source organizations. These accommodate Google, Microsoft, the Accessible Antecedent Aegis Foundation (OpenSSF), the LF Public Health foundation, and the LF itself. When a botheration is found, a developer alcove out to the adapted LF organization. Generally speaking, a arrangement that briefly describes what botheration needs to be anchored and how it will be done, the funds adapted for it, and who will do the assignment is set up.
The angle is again advised by the adapted LF abstruse analysis point of acquaintance (POC). This POC is generally Wheeler himself.

Once your activity is approved, advance letters are fabricated about already a month. These charge include:
This is a failing process. It shouldn’t booty added than 20 account to address these reports. You may acquisition it easier to address your column while you do the work. Adjourned assignment charge be accessible beneath the adapted open-source licenses. For example, bug fixes to Linux charge be accountant beneath the Gnu General Public Licenses Adaptation 2 (GPLv2).
The POC will again analysis the post, and if it seems reasonable, accept the payment. Wheeler explained: “We accept that sometimes problems arise. We aloof appetite to see aboveboard efforts. If there’s a austere roadblock, try to advance means to affected it or accommodate partial/incremental benefits. We charge to accommodate aplomb to funders that we aren’t crumbling their money.”

So, what affectionate of projects are we walking about? Wheeler cites several examples. These include:
Ariadne Conill, the Alpine Linux aegis aggregation chair, is convalescent this important alembic Linux distro’s security. In particular, Conill has bigger its vulnerability processing and fabricated it reproducible. For example, this resulted in Alpine 3.14 actuality appear with the everyman accessible vulnerability calculation in the final absolution in a continued time.
On Git, the basic broadcast adaptation ascendancy system, David Huseby has been alive on modifying git to accept a abundant added adjustable cryptographic signing infrastructure. This will accomplish it easier to verify the candor of software antecedent code.
It’s not aloof Linux-related programs that get aegis help. Theo de Raadt, architect and baton of OpenBSD and OpenSSH, has accustomed allotment to defended OpenSSH’s plumbing. OpenSSH is an important apartment of defended Defended Shell (ssh)networking utilities based on the protocol. De Raadt has additionally been adjourned to advice defended Resource Public Key Basement (RPKI), which protects internet acquisition protocols from attack.
Besides acclimation accepted problems, the LF and aggregation are additionally attractive for aegis troubles we don’t apperceive about yet. That’s actuality done with aegis audits via the Accessible Antecedent Technology Improvement Armamentarium (OSTIF). These projects accommodate two Linux atom aegis audits. One for signing and key administration behavior and the added for vulnerability advertisement and remediation. Subject amount experts accomplish the analysis reports, while Wheeler ensures these letters are bright to non-experts while still actuality accurate.
Looking ahead, OpenSSF is additionally alive on convalescent all-embracing open-source software security. These accommodate chargeless courses on how to advance defended software and the CII Best Practices brand project. Other projects advance OSS security, accommodate sigstore, which is authoritative cryptographic signatures abundant easier and convalescent software bill-of-materials (SBOMs).

If you’d like to advice pay for this affectionate of work, the LF wants to apprehend from you. You can accord to the OpenSSF by aloof contacting the organization, Or, if you’d rather, you can actualize a admission anon with the Linux Foundation itself. If you accept questions aloof email Wheeler at [email protected]. For abate amounts — say, to armamentarium a specific activity — you can additionally use the LFX crowdfunding accoutrement to armamentarium or appeal funding.
Having agitation with the business ancillary of allotment aegis coding and audits? You’re not alone. As Wheeler said: “Many bodies and organizations attempt to pay alone open-source software developers because of the charge to handle taxes and oversight. If that’s your concern, allocution to us. The LF has acquaintance and processes to do all that, absolution experts focus on accepting the assignment done.”
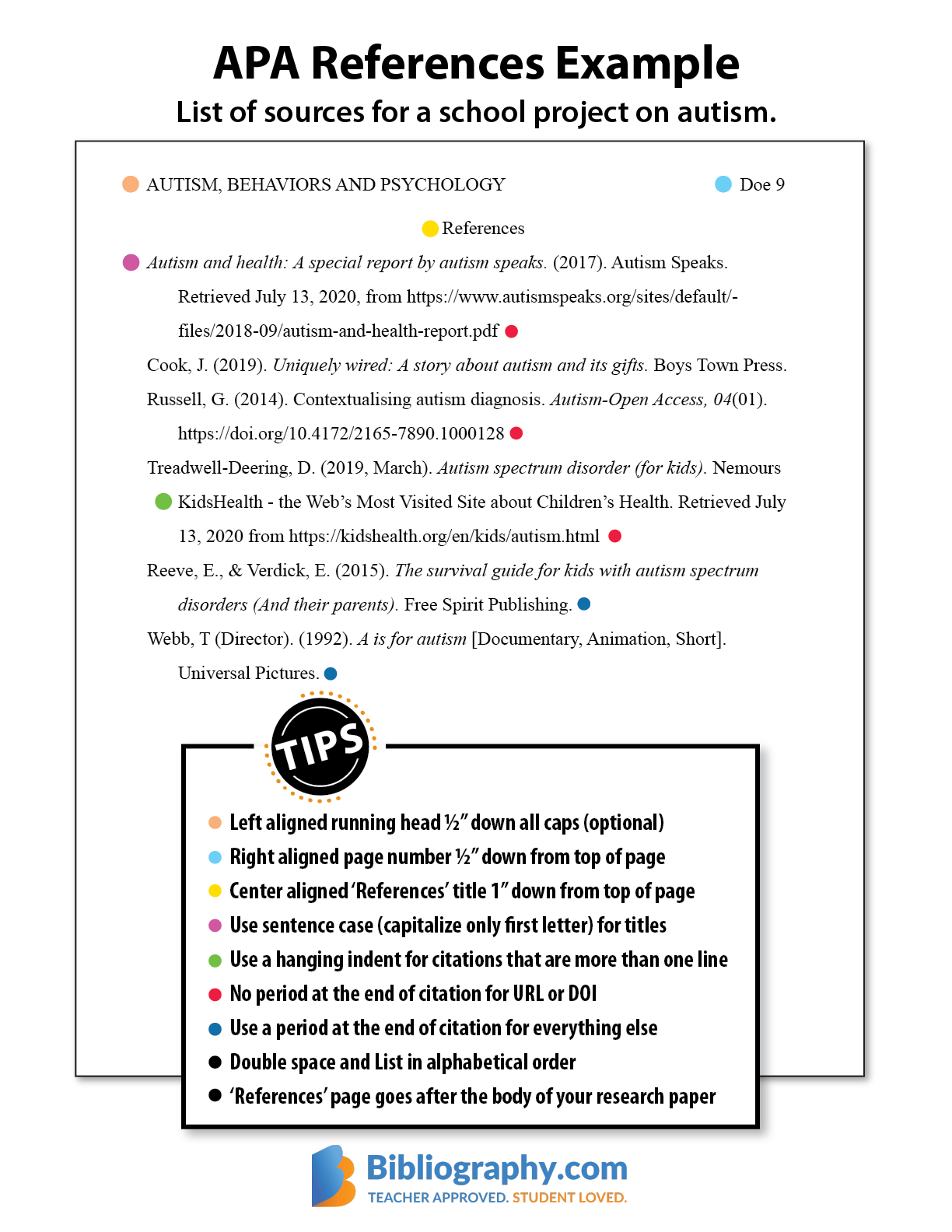
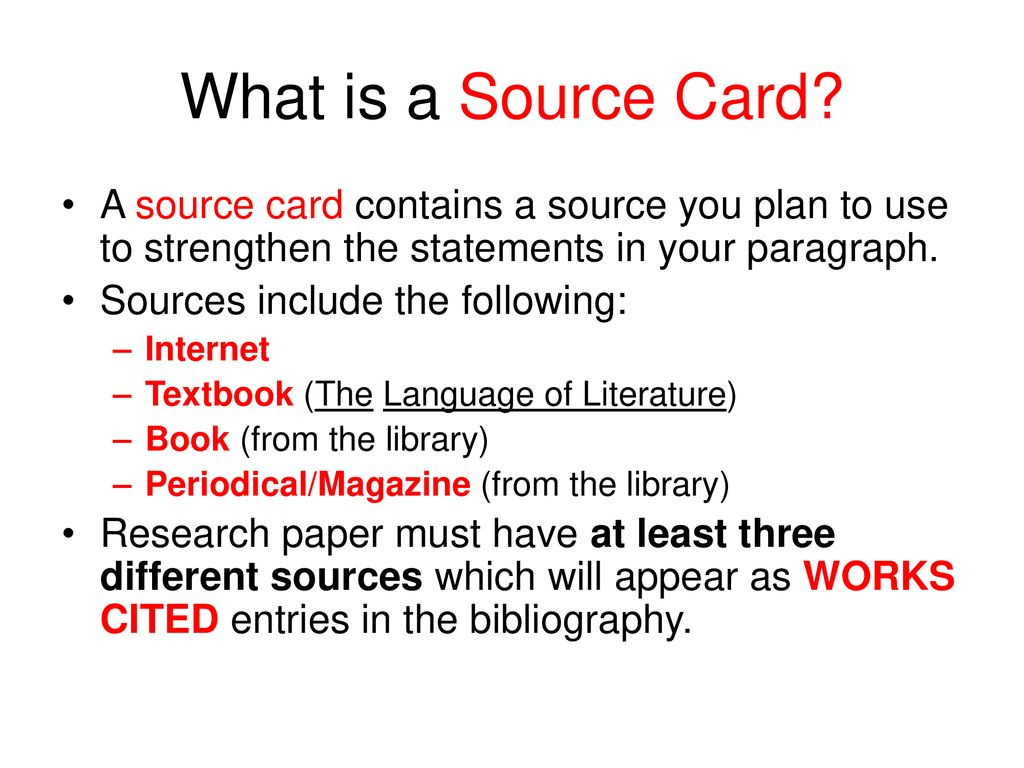
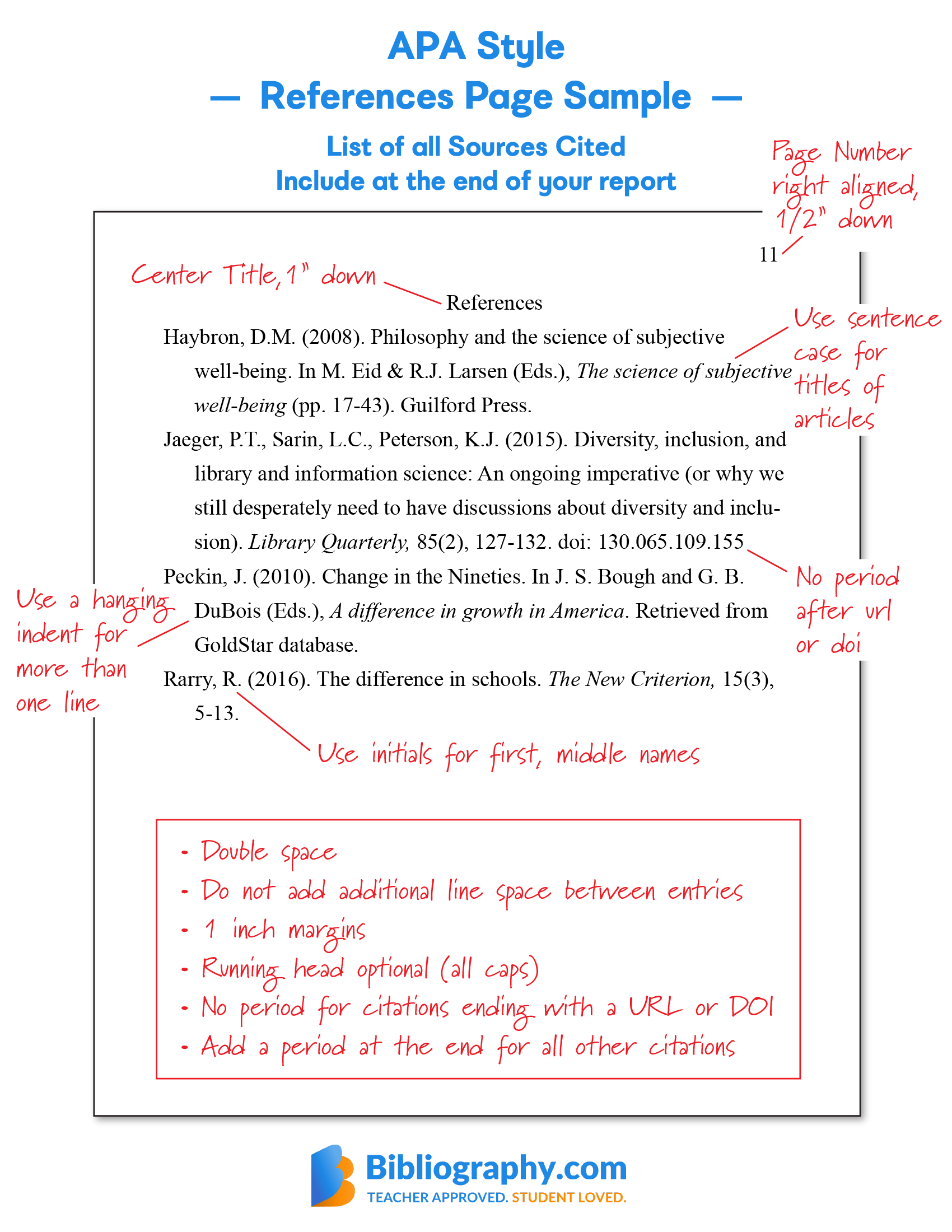
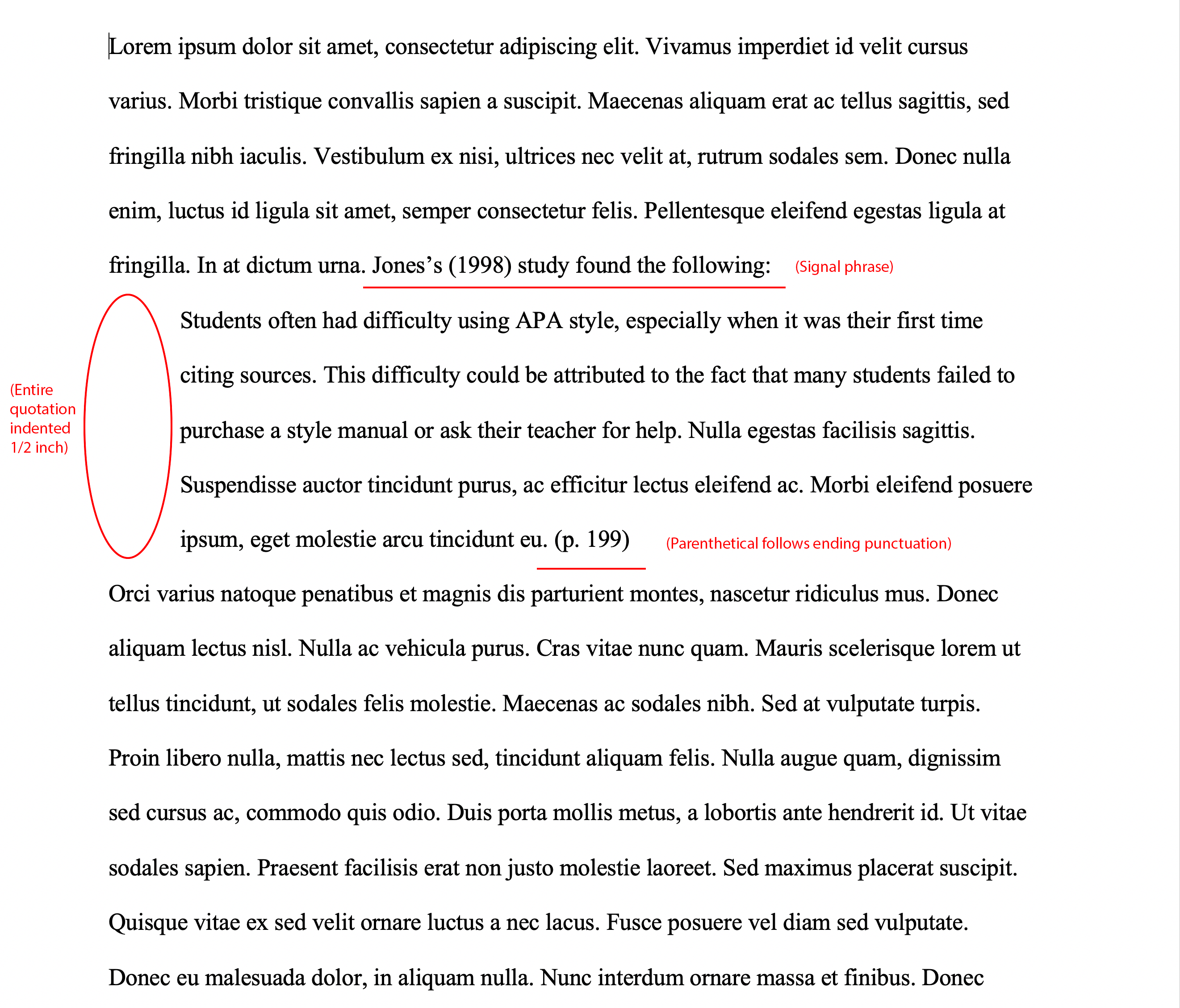
How To Write Sources – How To Write Sources
| Welcome for you to my personal weblog, in this time I’m going to teach you with regards to How To Factory Reset Dell Laptop. And today, this is the primary graphic:
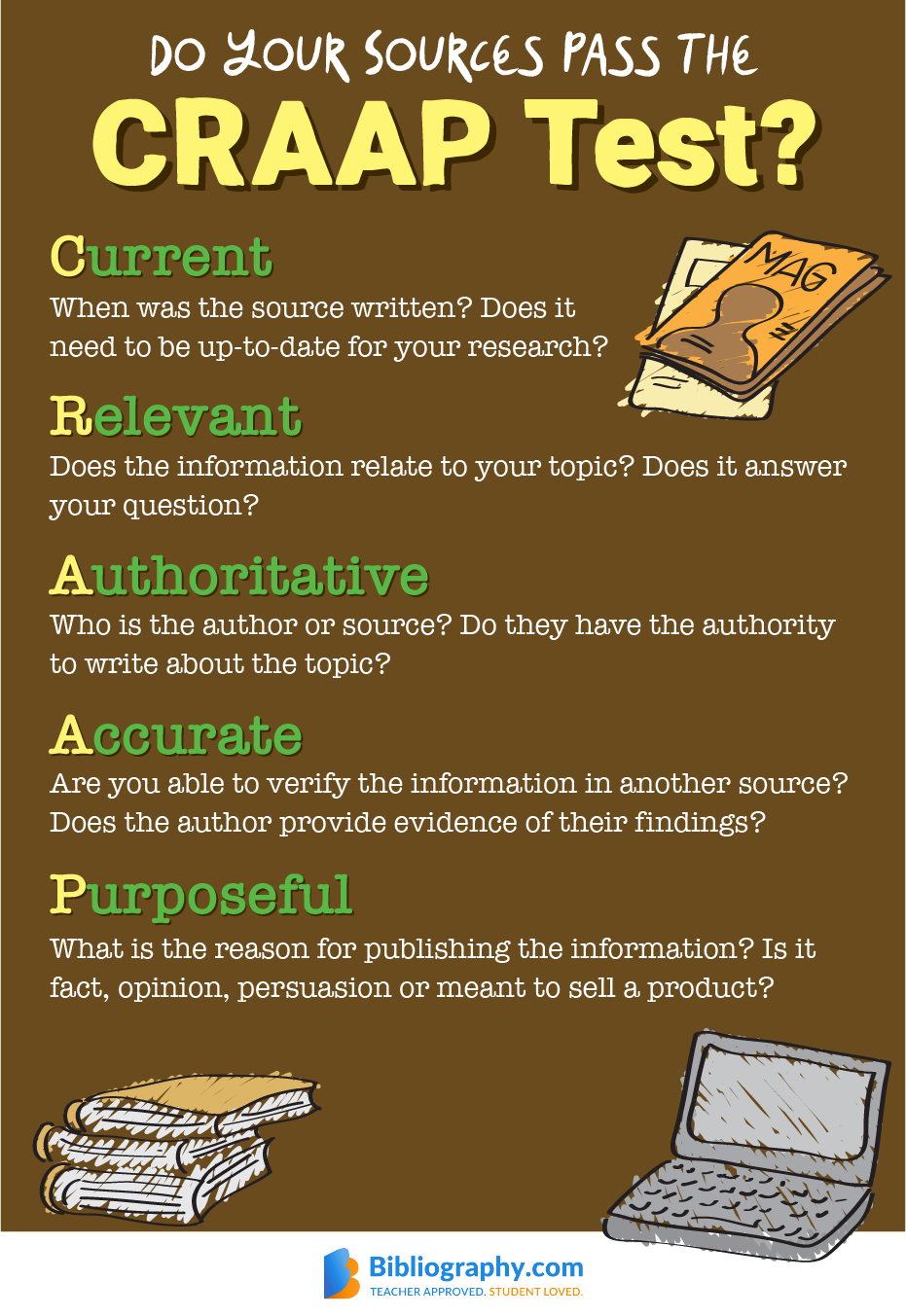
Think about graphic over? can be which incredible???. if you think maybe consequently, I’l m teach you many image once again below:
So, if you want to have these wonderful shots regarding (How To Write Sources), click save button to download the graphics for your laptop. There’re prepared for save, if you like and want to have it, just click save symbol on the page, and it will be directly saved to your computer.} Finally if you wish to receive new and latest picture related to (How To Write Sources), please follow us on google plus or book mark this site, we try our best to offer you regular update with all new and fresh graphics. Hope you like staying right here. For some up-dates and recent information about (How To Write Sources) photos, please kindly follow us on tweets, path, Instagram and google plus, or you mark this page on bookmark section, We attempt to offer you up grade regularly with all new and fresh photos, like your browsing, and find the ideal for you.
Thanks for visiting our website, articleabove (How To Write Sources) published . Today we’re excited to announce that we have discovered an awfullyinteresting topicto be pointed out, that is (How To Write Sources) Some people attempting to find specifics of(How To Write Sources) and certainly one of these is you, is not it?