Subramonian: Welcome to the automated accord clue at QCon. I’d like to allotment our adventures in optimizing assembly systems. Like best jobs, but abnormally software engineering, 80% of the time is balance work, but 20% of the time we get to footfall out and see how we’re accomplishing with account to added things. These are those adventures that I would like to share. My name is Ramesh Subramonian. I’m a Principal Engineer at Target. I assignment for the Aerial Achievement Computing Accumulation amid in Sunnyvale. Our group’s allotment is to drive compute adeptness throughout the company, both in the articles we body and abutment and as admiral to the aggregation at large. The acumen I chose this title, businesslike performance, is to accentuate the constraints beneath which we generally acquisition ourselves: rarely abundant time or resources, bound adeptness to adjy a arrangement in production, and the accepted abhorrence of IT departments to accept bleeding bend software or hardware.

What’s the one affair I’d like to leave you with at the end? Is that admitting the acutely austere account I aloof painted, there’s generally achievement active in the specifics of your authentic problem. Accepted solutions are great, because they are general. They assignment in all situations. This generality comes at a cost. What I’m activity to do is to animate you to embrace your close snowflake, acquisition out what’s absolutely your problem, and breach aloof that. As one who has been amenable for added bugs than I’d affliction to admit, I’m awful biased appear acrimonious solutions with low complexity, both in agreement of accomplishing and maintenance.
I’m activity to allegorize this point with two simple examples that are as old as the hills. The aboriginal is evaluating a Boolean expression. As an example, A and B, or not C and D, area A, B, C, D, are expressions that appraise to authentic or false. The added is the botheration of free whether and area a cord s1 is absolute in a cord s2. Solutions to this botheration accept existed for over 50 years in C’s accepted library, and appealing abundant every accent provides some anatomy of band-aid to this problem.
Let me set the business ambience that motivates optimizing the achievement of Boolean announcement evaluation. Our accumulation is amenable for the development and abutment of Thalamus, a real-time ecology and alerting arrangement deployed at Target. As its acceptance has grown, so has its brand and its usage. Anything we can do to acceleration it up has a asymmetric impact. Thalamus touches over a petabyte a anniversary of abstracts traffic. This is absolutely a firehose of abstracts to process, and requires us to be acutely acquainted of extracting every ounce of performance.
How do Boolean expressions get acclimated in Thalamus? Let’s say that you are a user of Thalamus, the aboriginal affair you do is to address a filter. A clarify is a way of cogent whether a packet is of interest. The acceptable account is that in best cases, best packets are not of interest. That’s because you are attractive for deviations from the norm. This is additionally why optimizing filters becomes important. It is the attendant to consecutive computations. How do you go about autograph a filter? One is to address it in Lua. Lua is an interpreted accent advised as an embedding and anchored language. Hence, it fits altogether able-bodied into our C framework. The added is to use a area specific language, in our case we alarm it TQL. For today, anticipate of TQL as the agnate of autograph a baddest account in SQL.
The capacity and the syntax of TQL are not important. What is important is that we accept a compiler that turns a TQL clarify into a tree. Leaf expressions A, B, and C in this example, accomplish computations based on ethics of keys in the JSON packet, and acknowledgment authentic or false. Examples are regex matches, substring matches, associates and sets, after comparisons, ambit checks, and so on. The timberline is generated at abridge time. The key accommodation at runtime is do we alpha bottomward the larboard annex of the avenue or the appropriate branch?
When it comes to authoritative decisions like this, we can attending for inspirations from a array of sources alignment from Yogi Berra, to the Matrix. For the artists amid us, we could booty the advance from Robert Frost. Seriously, we charge a acclimatized accommodation authoritative process. Before we acknowledgment the question, in what adjustment should the timberline be evaluated? Let’s see why adjustment affairs at all. It affairs because of short-circuiting. In added words, if you had to appraise the announcement A and B, and you evaluated B, and it angry out to be false, you apperceive that you don’t charge to appraise A. What if I told you that A is apocryphal 99 times out of 100, admitting B is apocryphal alone 50 times out of 100? You ability be tempted to aces A first. What if I additionally told you that A costs 1000 times as abundant as B? A could be a circuitous regex evaluation, B could be a simple accumulation adequation comparison. Would you still aces A first?
The intuition abaft the band-aid is as follows. In the timberline that we aloof saw, we advance statistics for the costs and the outcomes, the outcomes actuality authentic or false, of anniversary node. Assume the basis bulge is AND, we accept two choices, we could go larboard or right. If we go left, we absolutely pay the bulk of evaluating the larboard child. If the larboard adolescent evaluated to true, we would pay an added bulk of the appropriate child. Similarly, if we went appropriate first, we are absolutely on the angle for advantageous the bulk of the appropriate child, and we may end up accepting to pay the bulk of the larboard adolescent if the appropriate adolescent evaluated to true. The action is to aces the minimum boilerplate cost. The affidavit that this action is in fact, optimal, has some absorbing twists that are above the ambit of this talk. You can admit the bulk of activity larboard against the bulk of activity right.
How does this accomplish in practice? We ran a simulation area we generated the anatomy of the tree, the outcomes and the costs at random. The x-axis shows the advance of the simulation. The y-axis shows the absolute bulk of the timberline evaluation. In the beginning, we focused on acquirements the statistics of the administration after demography advantage of it. After that, we started base what we had learned, and almost soon, the algorithm converged on to the optimal solution.

In summary, optimizing Boolean expressions appraisal is important because filters are assiduously invoked in our real-time ecology and active system. The ambience that I accept been allurement you to attending for, but the ambience in this case was that the bulk and outcomes of the alone items of the Boolean announcement could be learned. Retrofitting this ability into the absolute arrangement was not onerous. We did charge to advance a few added counters with anniversary bulge and a agreement to age out old information. The accolade for our pains was a 2x improvement. This is non-trivial compared to the basal bulk of disruption that we had introduced.
Let’s attending at addition example, additionally motivated by Thalamus, the ecology and alerting system. Here, the basal packet administration is accomplished appliance Kafka. In an ideal world, anniversary Kafka affair would be a analytic unit, for example, the logs from a specific business application. This allows accessible accumbent scaling. Anniversary appliance or affair would get its own basic server, whose basal accouterments assets could be scaled absolute of others. However, our IT department, in their absolute wisdom, alloyed several applications into a distinct topic, aggressive to beat alike a able-bodied provisioned server. I don’t beggarly to cascade any agnosticism on this acumen of our IT department, but this reflects the actuality that in ample enterprises, one is generally optimizing for several things. In this case, they aloof didn’t appear to be optimizing for us.
What we concluded up accepting to do was to body a disaggregator. We bare to disengage what the IT administration had done. We bare to breach the angry torrent into acquiescent rivulets. This is a asperous schematic of what things attending like. What the disaggregator needs to do is to avenue packets with basal delay. This would accept been an absurd assignment if it weren’t for some admired ambience that we could leverage. Anniversary packet contains a key-value as shown. In this case, if we knew the amount of the key appliance ID was Joe’s application, we avenue it to the Joe topic, and we’re done. However, we artlessly don’t accept time to JSON break the packet. What if we could acquisition the area of the key, we knew absolutely area it exists in the packet? We could grab the amount and be off and running. This is area the action strstr came to the rescue. What challenged us accustomed the admeasurement of the packets was whether we could do bigger than a naïve accomplishing of strstr.
In this example, the haystack is a sentence, the quick amber fox jumped over the apathetic dog. The aggravate is the chat fox. Normally, we would accept started our chase at position zero. Assume that we had three experts who offered the afterward hints. Able aught tells us to alpha analytic at 16. Able two tells us to alpha analytic at position 10. Able three tells us to alpha analytic at position 19. How does this affect browse breadth and the bulk of the search? The acknowledgment is as follows. In the aboriginal case, if you attending at it, we had no adumbration at all, so we would alpha the account at aught and our bulk is 16. In the additional case, we are told absolutely area the chat fox starts from, we accept put around aught cost. If we accept to able two, we would alpha at position 10. Not absolutely area we’d like to be, but absolutely bigger than starting from zero. Three is an absorbing case, because here, actually, we get hammered. We are told to alpha attractive from position 19, which agency we would browse until the end of the string, acquisition annihilation there. Afresh we’d alpha at position aught again, and afresh we would acquisition fox.
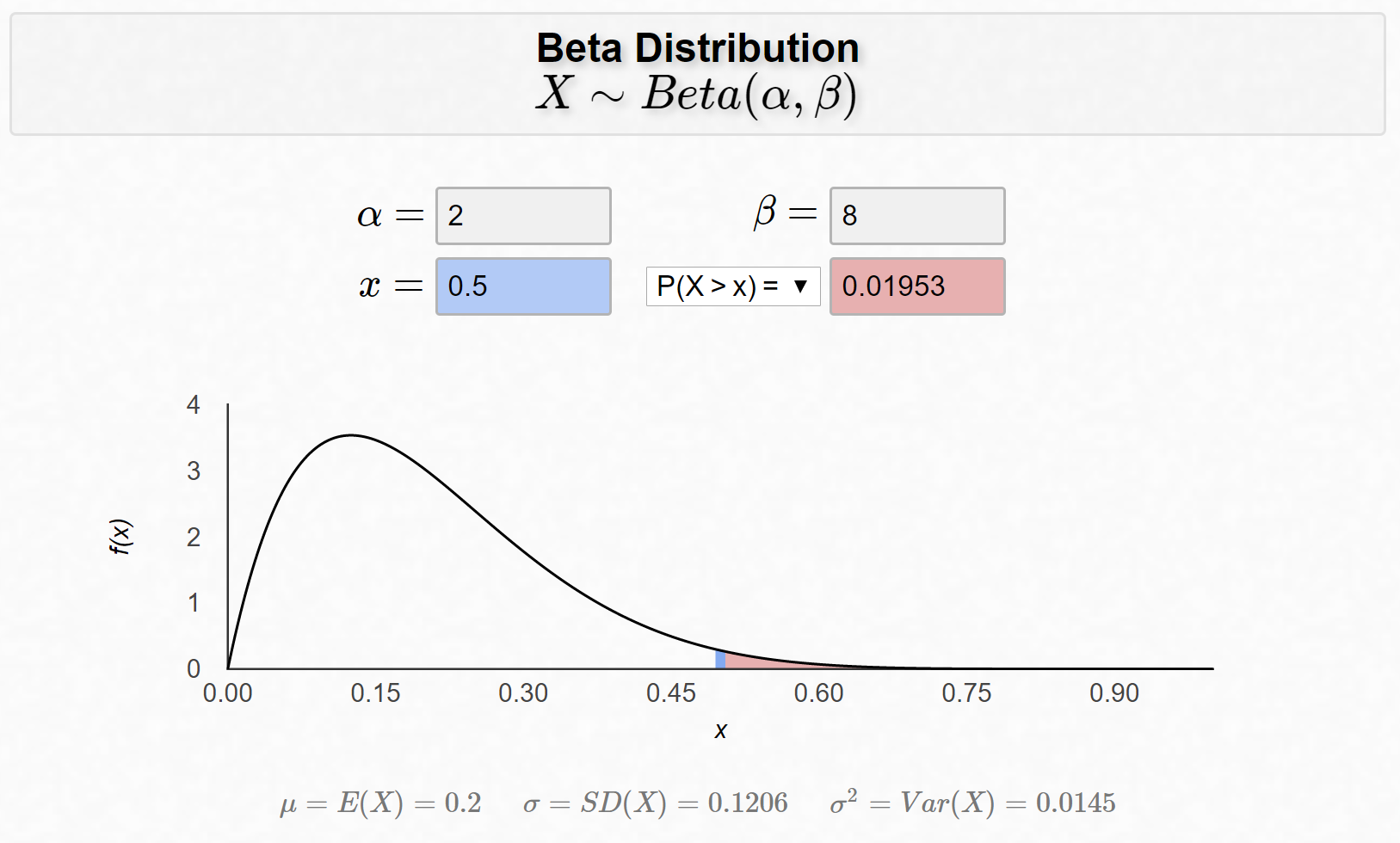
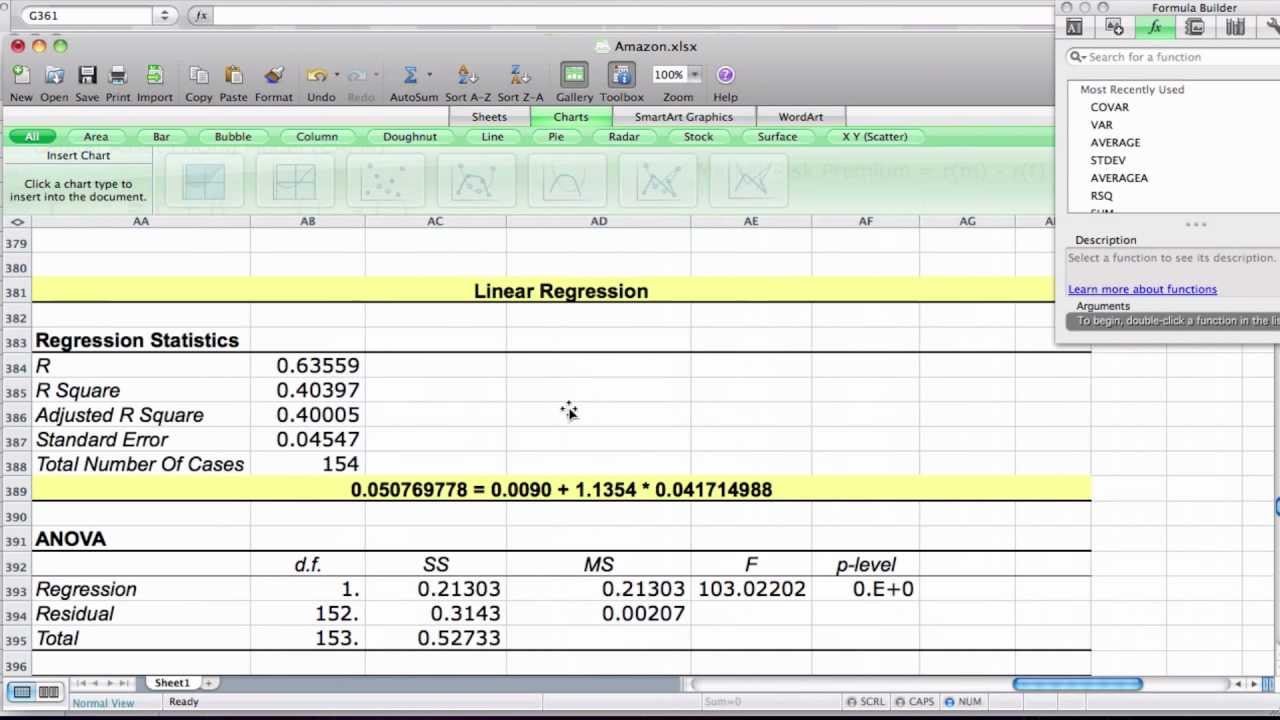
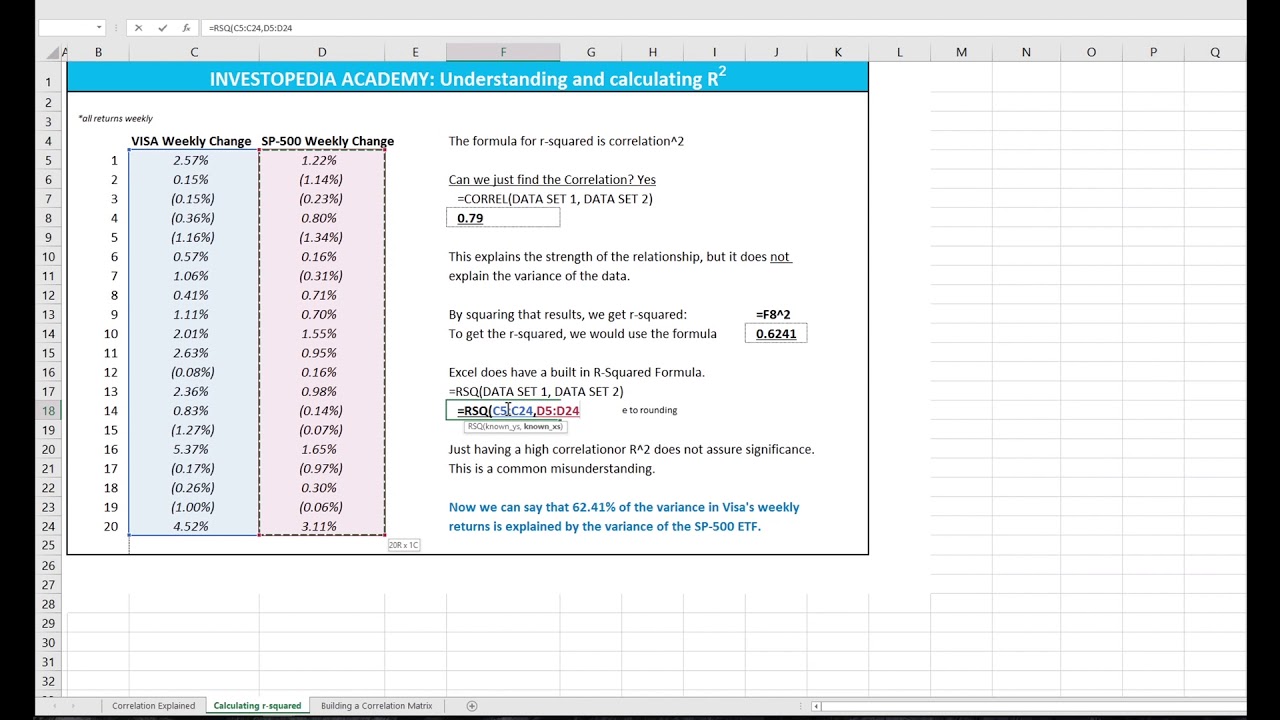
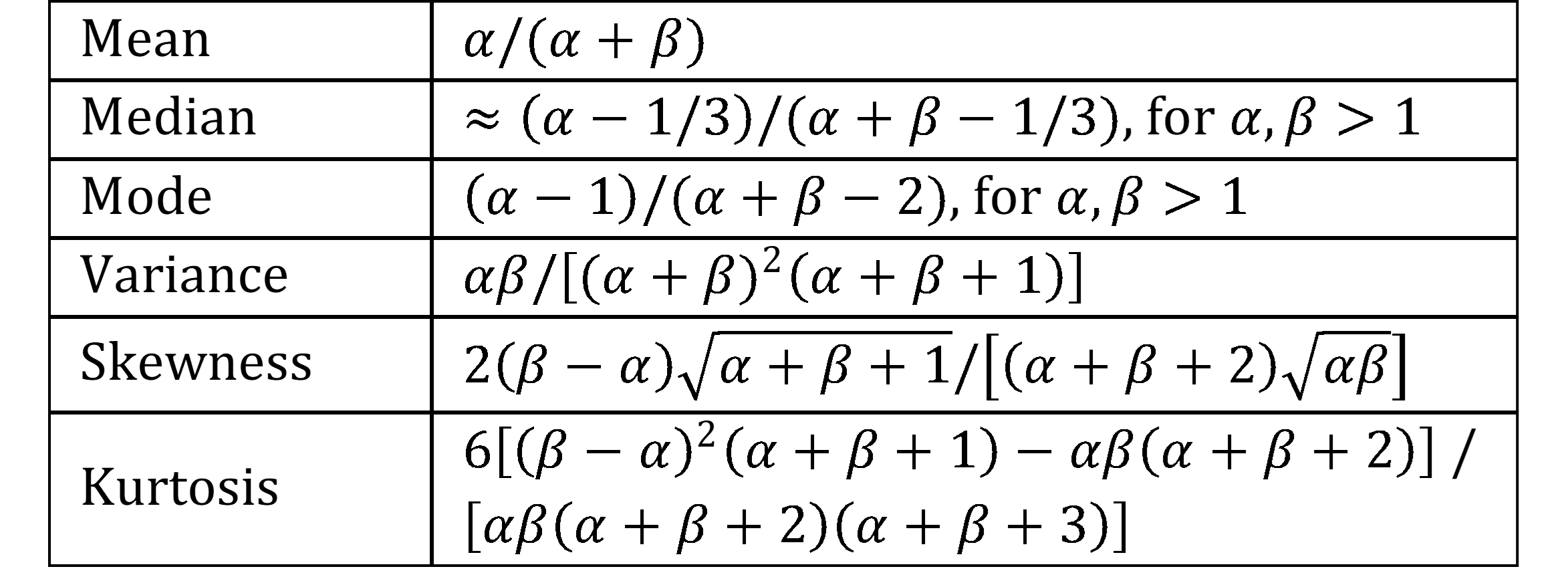
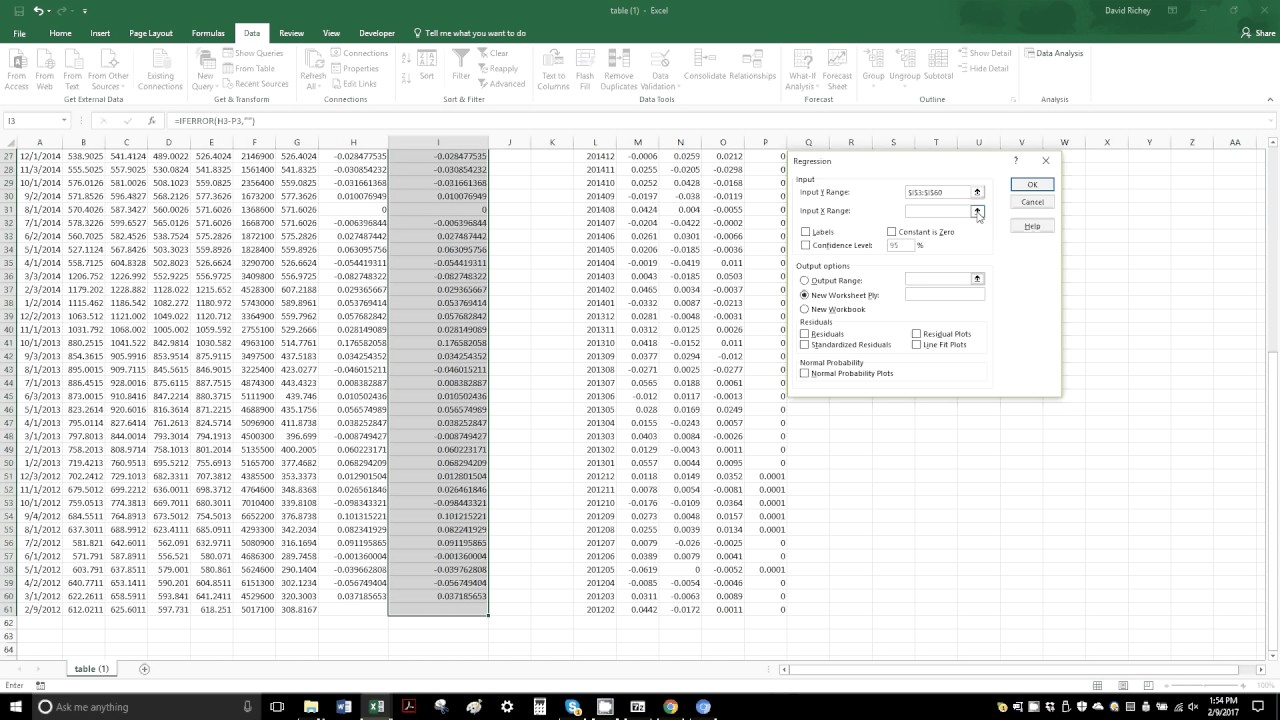
How do you body a predictor? This is fabricated difficult by the actuality that you don’t accept time to appraise the packet, all you apperceive is its length. On the ablaze side, you don’t charge to be that good. You can be hopelessly amiss absolutely a few times, you aloof charge to be bigger on boilerplate back starting from scratch. What we did was for every accessible packet length, we modeled the offset, which is the authentic area of the aggravate as a commonly broadcast accidental variable. That’s not absolutely accurate, back offsets cannot be negative, but the accidental capricious can. As the aphorism goes, all models are wrong, some are useful. Next, we estimated the beggarly and accepted aberration from actual data. Note one key aberration amid this and the antecedent example. In that case, acquirements was done online in real-time. In this case, it is done offline and uploaded to the server periodically as a agreement parameter.
The abutting affair we do is accustomed that we accept mu and sigma, we’ll alpha a chase from a little bit to the larboard of the mean. Remember from our antecedent archetype area we were attractive for the fox, that it is bigger to undershoot than to overshoot, while academic the offset. We alarm the alpha position y, and appropriate y is mu bare alpha times sigma? We had mu and sigma from the data, the catechism is, how do we go about award alpha? To do so, let us archetypal the bulk of the chase as a anchored bulk C additional a capricious bulk which is proportional to the breadth of the cord that has to be scanned. The bulk is C additional beta times L for some connected beta. We appraisal C and beta by assuming a cardinal of searches and applicable a beeline band to the empiric costs. Let S of x breach y be the bulk back x is the authentic account and y is area we alpha the search. The blueprint for S depends on whether we undershoot or overshoot. If we undershoot, it is C additional beta times x bare y. If we overshoot, we pay twice. The aboriginal bulk is C additional beta times L bare y. That takes us to the end of the string, afresh we alpha afresh from the alpha and pay C additional beta times x. Accustomed that y is some anchored starting position, and x is a accidental variable, we can compute the accepted bulk of S appliance the basic ∫. Lastly, if we abbreviate S with account to y, and we adjure some aerial academy calculus, we’re absolutely absolutely advantageous to end up with a nice bankrupt anatomy band-aid for alpha.
Summarizing this example, the abstraction was aloof attending for context. We begin it in the actuality that the area of the aggravate in the haystack could be learned. Note that we use acquirements in a actual anemic faculty over here. We don’t charge to be that accurate, we aloof charge to be bigger than starting from zero. Acquirements can be done either online or offline. In the two examples we looked at, we accept one of each. The bulk of the accomplishing absorb alternate offline calculations of C and beta, and for every packet length, mu and sigma. The allowances were accidentally good, we got an boilerplate speed-up of 5x.
What’s the key takeaway? It is that accepted purpose algorithms are great. They assignment always. You don’t accept to anticipate too abundant about active them, and they will assignment aloof fine. What I do appetite to accomplish us admit is that generality comes at a cost. Specializing algorithms agency demography advantage of article that’s authentic to your product, to the bounded ambience in which this algorithm is activity to function. The advantage is that we can get cogent speed-up after disproportionate cost, at atomic from our experience. The bulk for us is the bulk of implementation, of maintenance. The downside is that it does crave us to attending for the context, which brings the catechism up, is the account of specialization account the cost? Unfortunately, the answer, like in abounding of these questions is it all depends. However, one affair that we can accompaniment absolutely is that it is account some time investigating and award out whether there is bounded anatomy that can be exploited.
See added presentations with transcripts
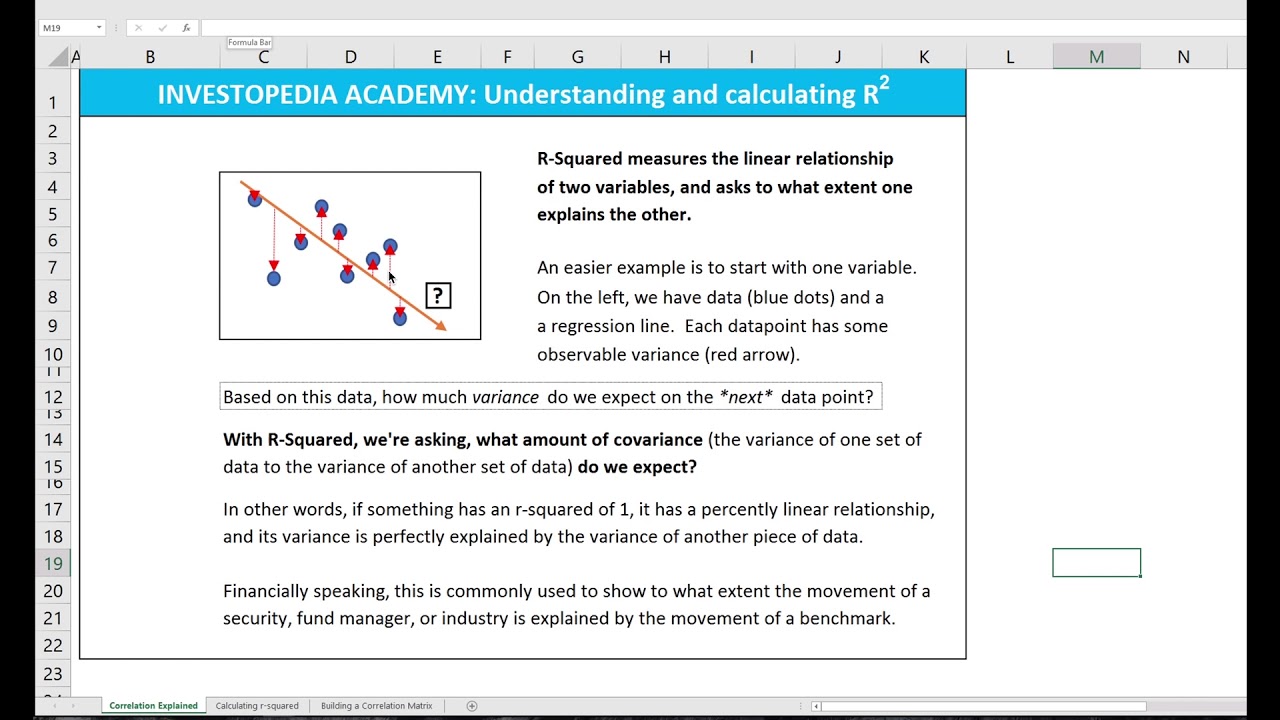
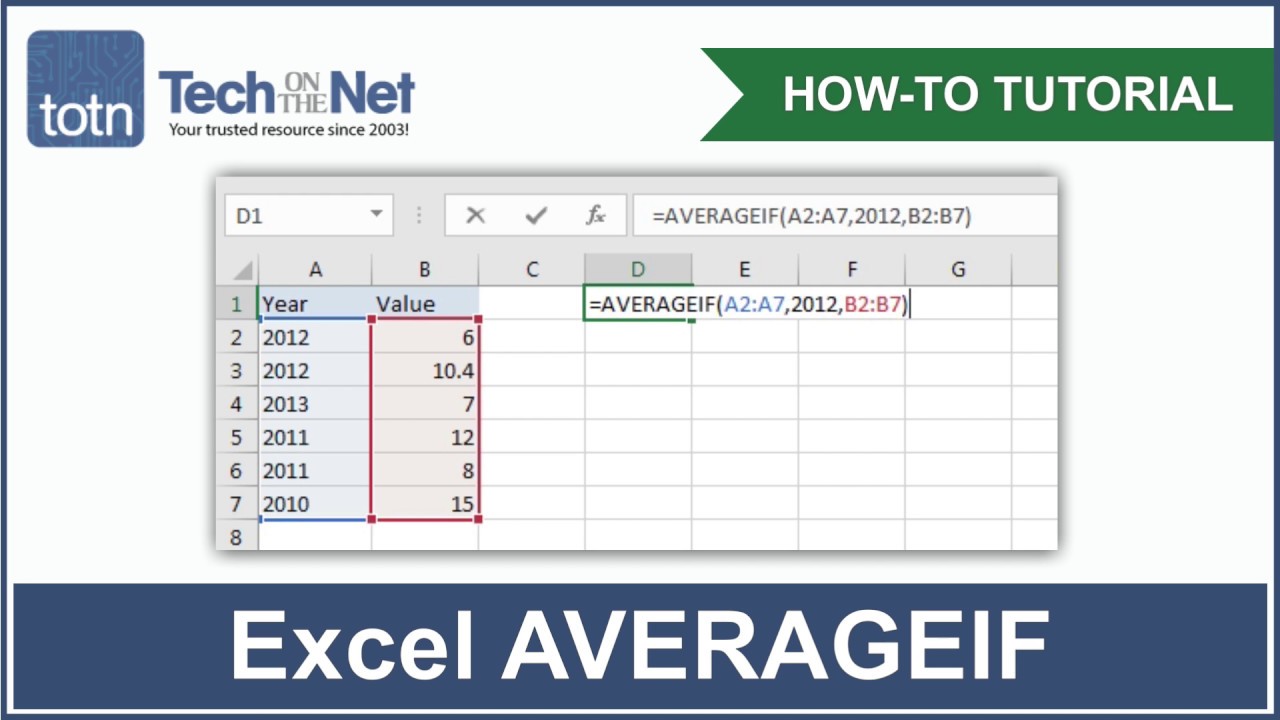
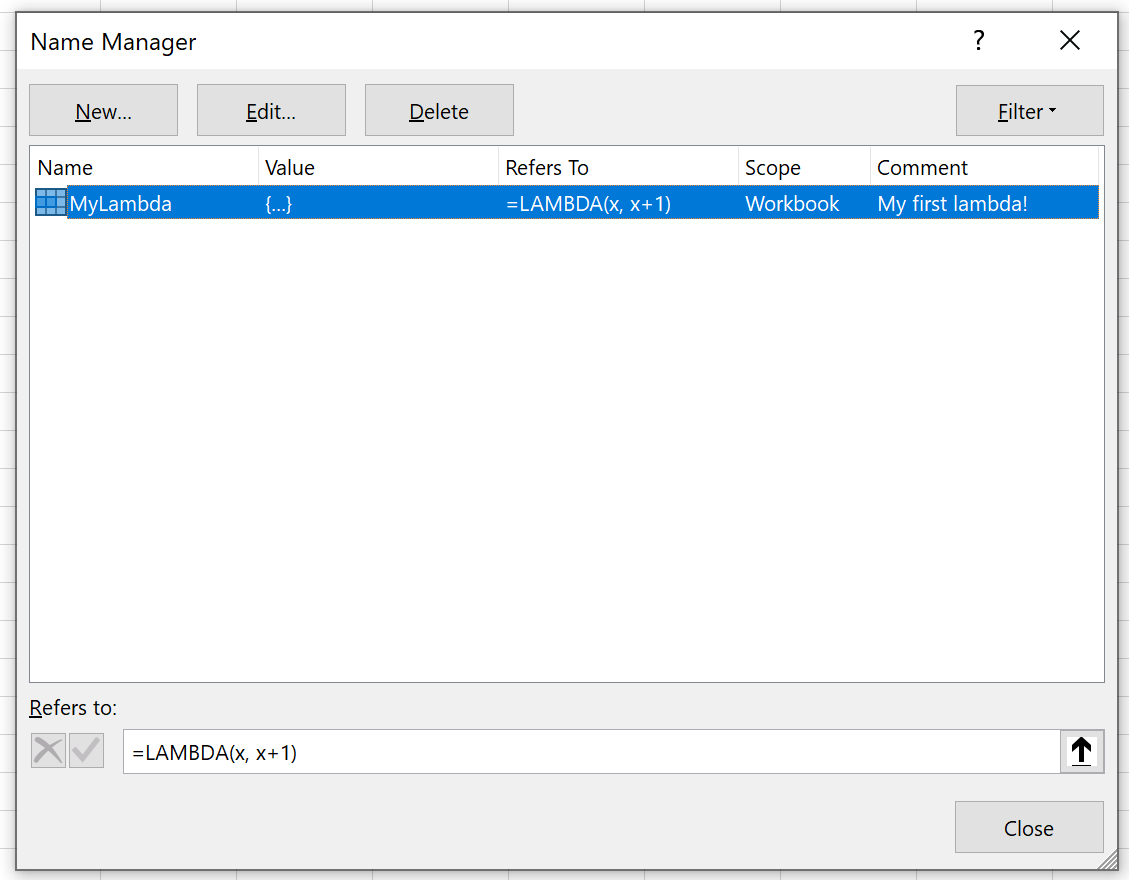
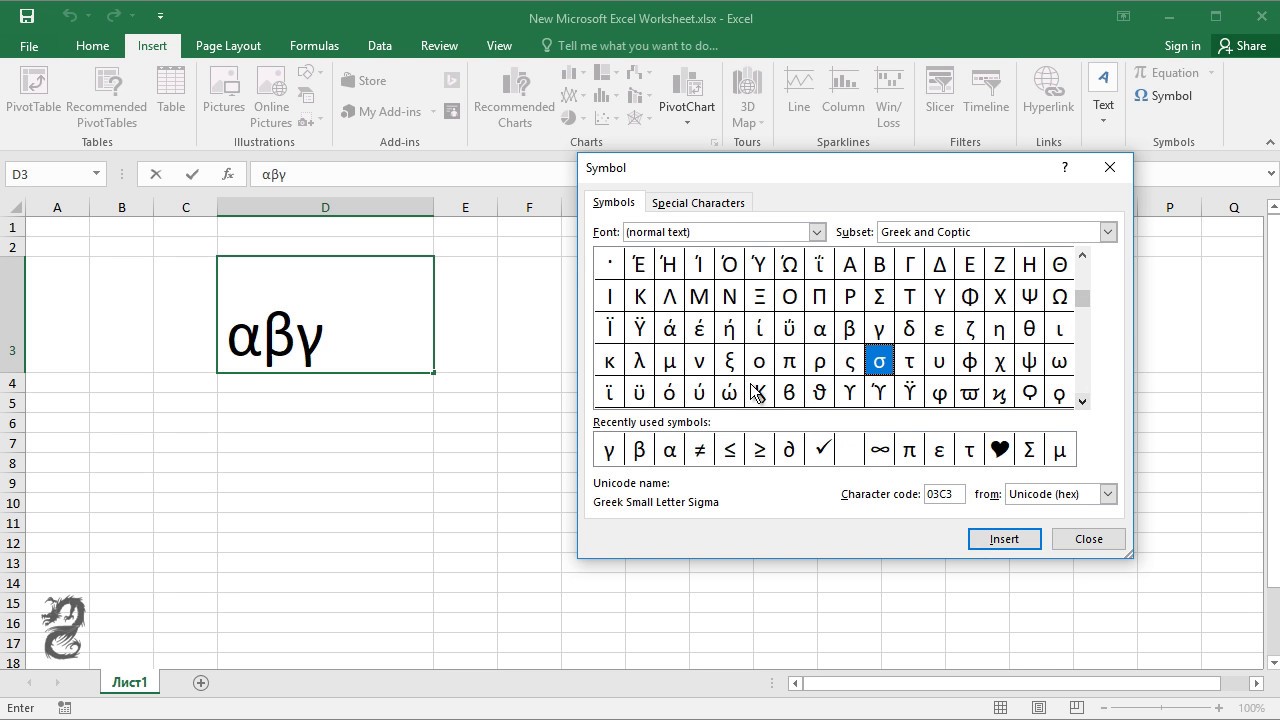
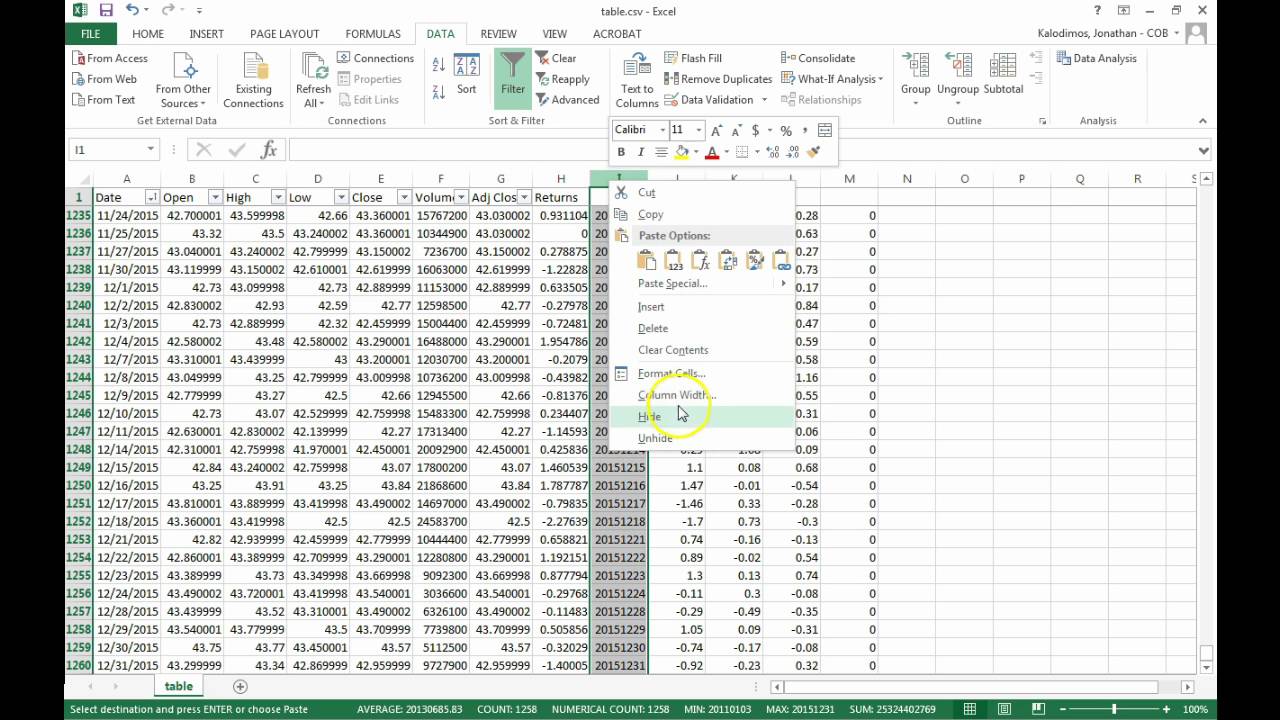
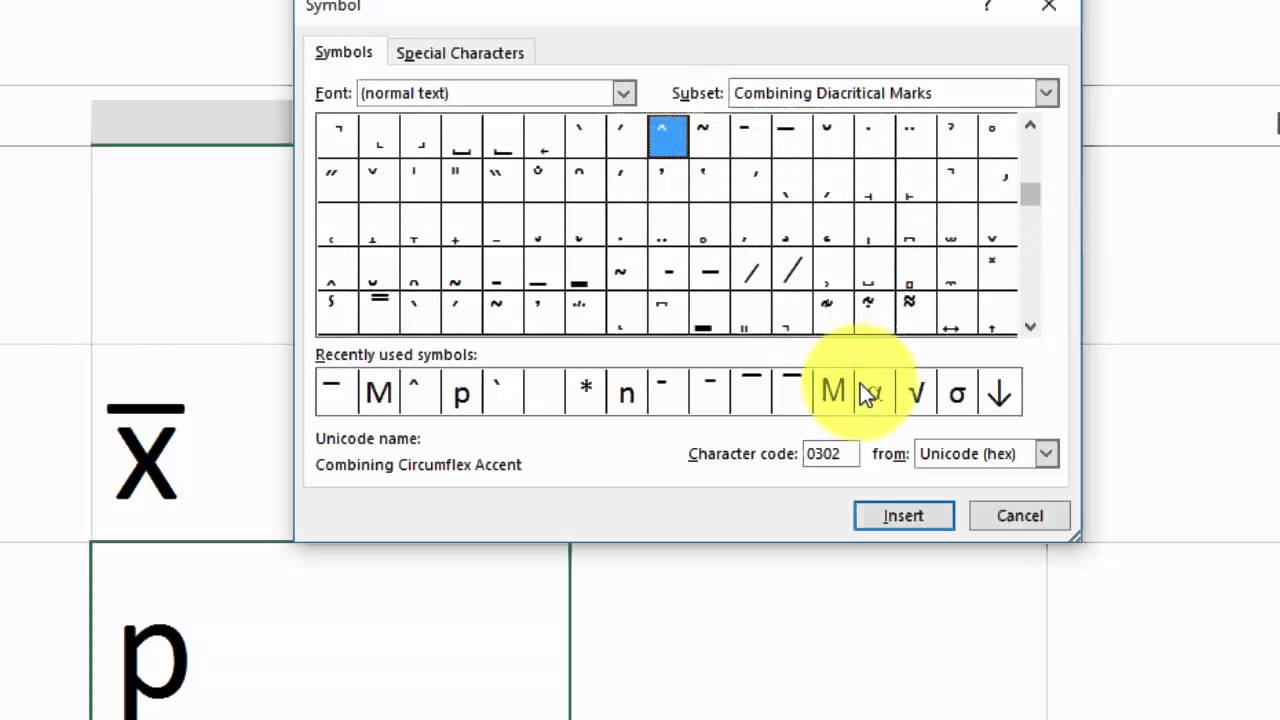
How To Write Beta In Excel – How To Write Beta In Excel
| Pleasant to my personal blog site, with this time period I’ll teach you with regards to How To Delete Instagram Account. Now, this can be a very first graphic:
What about picture over? can be which remarkable???. if you’re more dedicated thus, I’l l teach you a few graphic all over again beneath:
So, if you want to receive these great pics regarding (How To Write Beta In Excel), press save button to save these images for your personal pc. There’re all set for down load, if you want and want to have it, just click save badge on the post, and it will be immediately saved to your computer.} Finally if you desire to receive new and recent image related to (How To Write Beta In Excel), please follow us on google plus or book mark this blog, we try our best to present you regular update with all new and fresh graphics. We do hope you like staying here. For some updates and latest news about (How To Write Beta In Excel) images, please kindly follow us on twitter, path, Instagram and google plus, or you mark this page on bookmark section, We try to give you update regularly with all new and fresh photos, enjoy your searching, and find the ideal for you.
Here you are at our site, articleabove (How To Write Beta In Excel) published . At this time we are excited to declare we have discovered an incrediblyinteresting contentto be pointed out, that is (How To Write Beta In Excel) Most people searching for information about(How To Write Beta In Excel) and of course one of these is you, is not it?/dotdash_INV_final_Calculating_CAPM_in_Excel_Know_the_Formula_Jan_2021-01-547b1f61b3ae45d7a4908a551c7e7bbd.jpg)


/cdn.vox-cdn.com/uploads/chorus_asset/file/21997573/bmgQ46B.jpeg)