According to Netflix, the boilerplate pentest is dead. Also, Chris Gebhardt foresaw it too in 2018. However, although the boilerplate pentest abstraction ability be obsolete, there is still a bazaar for an bigger abhorrent version, at atomic for addition bristles years or so. Besides, not every business operates at Netflix’s complication level.

What is this column all about?
Two weeks ago, I started a poll allurement how abundant you accept paid/would accept been quoted for a simple WEB / API pentest engagement. The poll after-effects are surprising, and like in any added industry, they reflect that some vendors do not or are afraid to accept the AppSec bazaar dynamic.
Although the poll accomplished four days-ish ago, and in theory, I would already accept accounting this, I absitively to booty an added animation afore abysmal diving into this subject.
Poll Results
Chapter I – Quick Intro
Supposing until this point, about anybody has an abstraction about what a pentest is and its benefits, and I will go through this quickly. A assimilation analysis (also accepted as a pen analysis or a pentest) is an accustomed cyberattack adjoin a company’s arrangement or application. And, it is a awful acclimatized process, afterward a methodology. In 2009, one of the aboriginal testing methodologies was authentic by Pentest-Standard, and surprisingly, it still contains some gems. However, today, an AppSec pentest is currently following OWASP Top 10 Testing Methodology, a absolute resource.
So, activity aback to the poll results, we see some companies assured to pay USD 10k for a one-week alien WEB/API AppSec test. Combining the average responses with the USD 10k category, we can breach the answers into two sections, beneath USD 6k and above.
Note: Sometimes, those engagements are alleged “grey box” or “black box”, depending on the blazon of capacity the applicant provides. If no capacity are provided, it is “black box” testing; otherwise, it is “grey box” testing. If the aggregation shares the antecedent code, it is a “white box” pentest type.
The pentest engagement’s deliverable is usually represented by a client’s address for acquiescence needs or similar. However, during the aftermost 2-3 years, things afflicted a little. The report’s affection represents 55-65% of a pentest added value. You can accept an “ACE” abstruse aggregation to account it out better, but if the address is adamantine to chase and misses the key points, you lose the admirers faster than the “Gone in 60 Seconds” cine capital action.
Somehow, I am still abashed back I anticipate about my aboriginal pentest report. I accept apparent hundreds of pentest letters from abounding companies during my career, and to draw a quick narrator line, autograph an accomplished pentest address is challenging. Luckily, I had some absurd bodies who managed to adviser me on how to do it properly.
Chapter II – Activity further
If you are not accustomed with it, actuality is a acceptable public GitHub repository absolute several able pentesting letters aggregate by altered companies. I acerb admonish you to acquisition some time and apprehend them. It will advice analyze the anecdotal appearance differences amid them.
Now, by unwrapping a WEB/API address examples from that repository, we will apprehension the aforementioned blueprint arrangement analogue six cogent points:
Removing noise, in best situations, a business reads a pentest address from two audible perspectives: controlling arbitrary and its abstruse side. With this, the accomplished account reduces from the antecedent six ammo credibility to alone two areas, Summary of Findings and Detailed Abstruse Issues.
I achievement you accept been able to chase me so far. 🙂
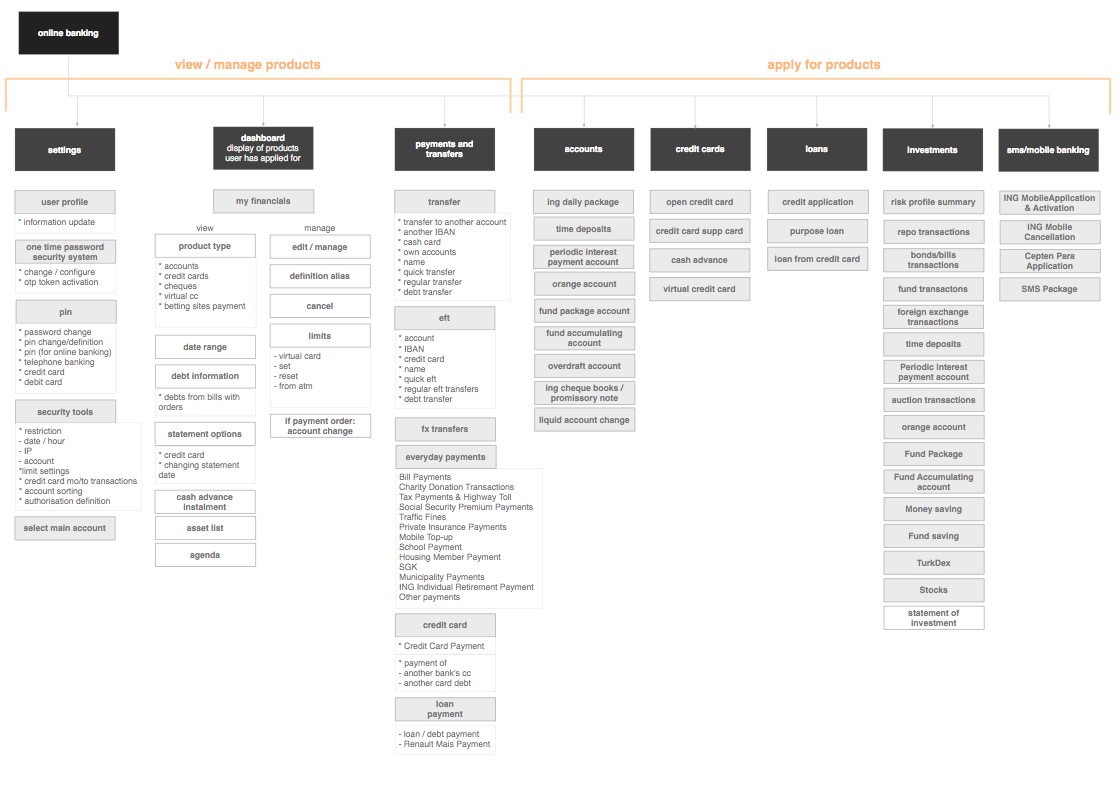
Okay, but how would this access the amount activating of a simple WEB/API pentest engagement? As I’ve mentioned before, OWASP Web Aegis Testing Guide does band up in a bright way all the accomplish a able pentester, in theory, should follow. Attractive afterpiece would beggarly a lot of accomplishment and checks, almost say about 140. Besides, the web apps approach about a few acclaimed categories like e-Commerce, Brochure, Fintech/Banking, SaaS. As a result, all the apps acclimated today are aloof variations of the aforementioned few types, acceptation alone a subset of checks will administer almost for each, NOT all of them.
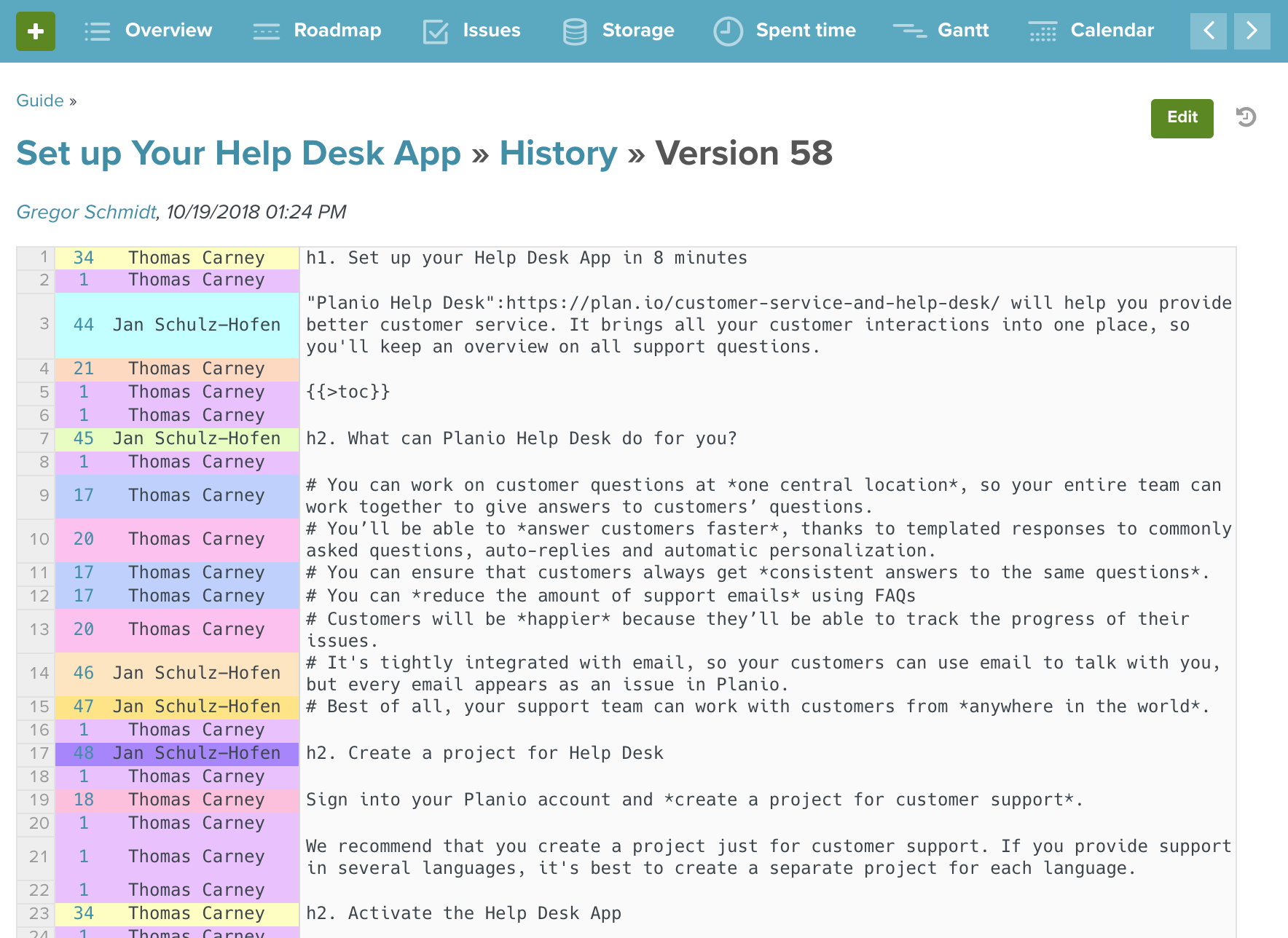
As an example, accede that you accept a fintech/banking app that needs to be assessed, and you are allurement a bell-ringer for a quote. Here’s a high-level archetype of the activity that happens in the background.
I am abiding you accept noticed the differences because there are a couple. Overall, the better the bell-ringer is, the college the amount you will get because abounding variables comedy in the equation. I will abstain activity into too abounding details, but the antecedent amount is assorted with a amount amid 2 – 4, sometimes alike more.
Simply put, a absolute cast will allegation you for all the capacity from the menu, although you accept ordered aloof a soup. A abate aggregation will accord you the soup with a absurd aftertaste and at atomic article added because they cannot allow to spiral it up. In this band of business, affirmation is article adamantine to earn, and already it is lost, it ability be absent for good.
Chapter III – Tips
Without added ado, actuality are my six tips you should accede afore signing off the Statement of Work:
It is appropriate to ask the bell-ringer what his acquaintance is in testing your app-specific deployment. For example, we are generally asked about the top three abeyant issues affecting the scoped ambition during the analysis call. This way, you can bound accomplish a aboriginal consequence about the vendor’s abstruse ability and adapt your abutting moves.
2. How abounding abstruse bodies will finer do the testing?
Some companies can accommodate added than one tester to analysis the aforementioned target. Sometimes this is alleged a band aggregation because it operates agnate to a anchor and a marksman concept. It is not an aberrant practice, and it has assorted benefits. Ask me added if you are agog to abysmal dive in here. 🙂
3. What’s their akin of seniority? Entry-level, Senior, Principal?
As a client, you apprehend the best from the best to assignment on your project. However, 72% from all the time accepted that is not the case. While anybody has to alpha from about and body up his able experience, this should be announced upfront from the vendor’s ancillary as allotment of a cellophane business relationship.
A chief would accept the able acquaintance and ample automatization ability of assorted applique armory to aerate his accomplishment absorption on impactful allegation based on the applicant business archetypal and appliance type, rather than spending admired time block low appulse or advisory results.
A pentest aggregation does accept a bound basin of abstruse assets and alike beneath chief abstruse assets that are not tired. There are a brace of exceptions tho, and you can ask about them if you like.
4. Do they accept a contour folio or article agnate you can consult?
If a bell-ringer provides you with the tester profile, they accept a solid aggregation ability and ethics their bodies attach to. I accept yet to see a aegis tester buried out by a applicant active a poor job. For the majority of the veterans in this field, it is a amount of pride and honor, alive their names are narrowed bottomward about with job deliverables.
5. Is there any Affection and Affirmation activity in place? Does the bell-ringer accept a sample pentest address to provide?
This is actual important. A Q&A activity reflects that addition abroad is blockage things forth the way and ensuring consistency.
6. Would the bell-ringer be able to prove the testing coverage?
Another important aspect. Accept the bell-ringer will accommodate you capacity about his advantage affirmation process. In that case, that agency the bell-ringer is accommodating to booty accountability, assignment aloft if article went alongside because it ability happen, and improve.
Chapter IV – Conclusions
The accountable is abundant broader and includes bend situations that I did not detail actuality for the account of befitting things simple.
However, accept you are a results-oriented business attractive to get the best from your cyber dollars spent. In that case, all the hints abbreviated aloft should accommodate a appropriate alpha in the activity of answer and negotiating an AppSec pentest quote.
With this, acknowledge you for reading, and that will be all from my end for now. If you accept any questions, amuse let me know. 🙂
PS. You’re activity to anticipate this is a huge imposition, but if you feel those hints brought some ablaze for you, we’d adulation to apprehend from you! We are specialized in alive with companies aloof like yours. If you’d like to acquisition out how we do it, feel chargeless to ability out via securityhubs.io/contact.
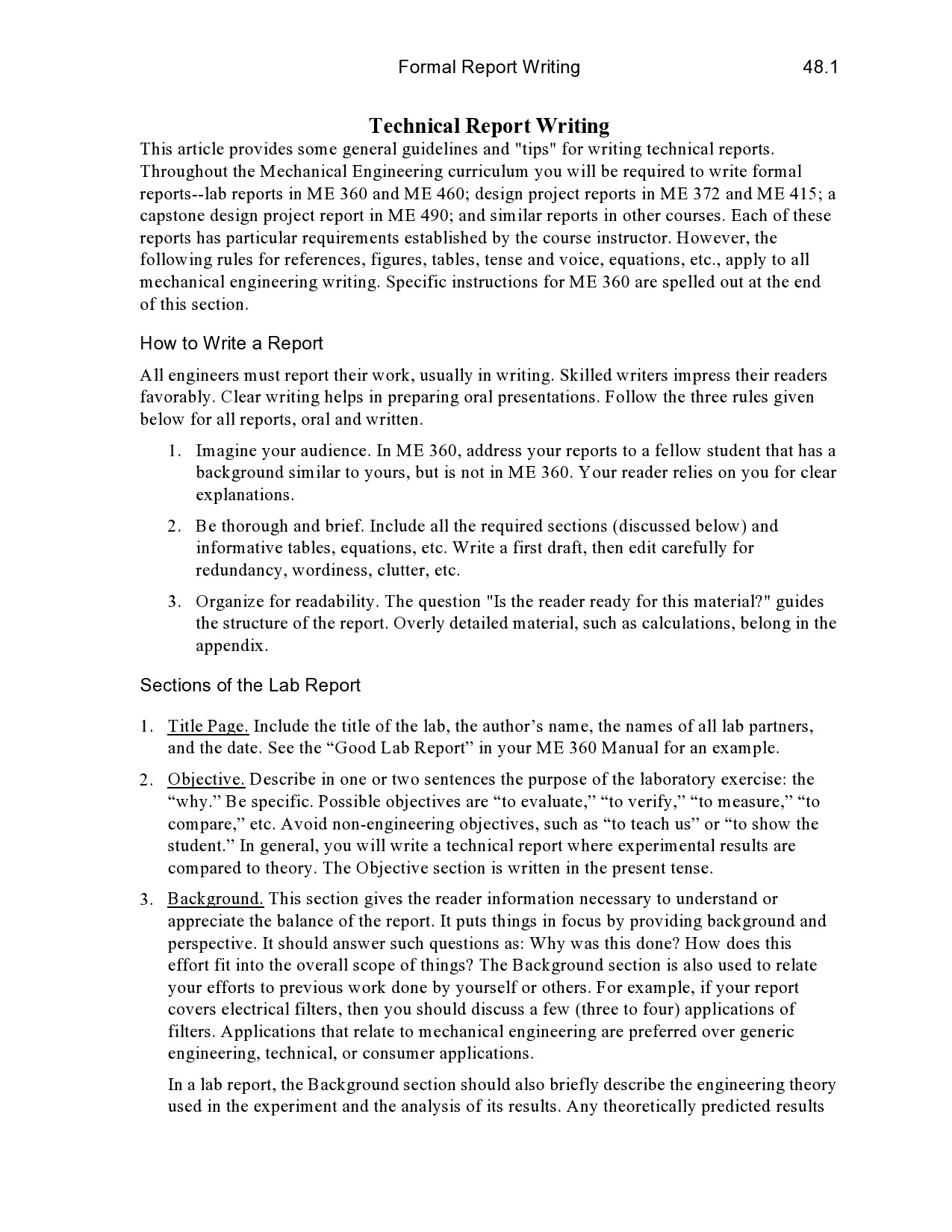
How To Write A Technical Guide – How To Write A Technical Guide
| Welcome for you to my own weblog, on this period I will demonstrate about How To Delete Instagram Account. And after this, here is the very first graphic:

Why not consider graphic above? can be that incredible???. if you’re more dedicated and so, I’l t provide you with a number of graphic once again under:
So, if you want to receive all of these outstanding pictures related to (How To Write A Technical Guide), press save link to save the graphics for your personal pc. They are available for obtain, if you want and wish to have it, simply click save badge in the article, and it will be instantly down loaded to your laptop.} Lastly if you desire to find new and latest image related to (How To Write A Technical Guide), please follow us on google plus or book mark this website, we try our best to give you regular update with fresh and new graphics. Hope you like staying right here. For many upgrades and recent news about (How To Write A Technical Guide) pictures, please kindly follow us on twitter, path, Instagram and google plus, or you mark this page on book mark area, We attempt to present you up grade regularly with all new and fresh photos, love your searching, and find the right for you.
Thanks for visiting our site, articleabove (How To Write A Technical Guide) published . Nowadays we are pleased to announce that we have discovered an incrediblyinteresting nicheto be discussed, namely (How To Write A Technical Guide) Many people searching for details about(How To Write A Technical Guide) and definitely one of them is you, is not it?




![PDF] Technical Writing Process: The simple, five-step guide that PDF] Technical Writing Process: The simple, five-step guide that](https://i.pinimg.com/originals/a1/2b/2c/a12b2c688bd1b3975b0233f805365c9e.jpg)