For added than two decades, Lorraine* has accepted her ex-boyfriend is watching her. She cut acquaintance with him 20 years ago, but in Facebook posts and alarming emails, he makes abiding she knows he’s still befitting tabs, from the bearing of her accouchement to her best contempo bells anniversary. Afterwards years of corruption that resulted in a PTSD analysis and acute nightmares, the addendum are chilling, and accomplish her afflictive putting any claimed admonition in an online amplitude area he could see it.
/cdn.vox-cdn.com/uploads/chorus_image/image/65226861/HowToErase.0.jpg)
“It’s afflicted my accord with my friends,” Lorraine says. “It’s afflicted my accord with my partner. It’s afflicted my adeptness to feel safe.”
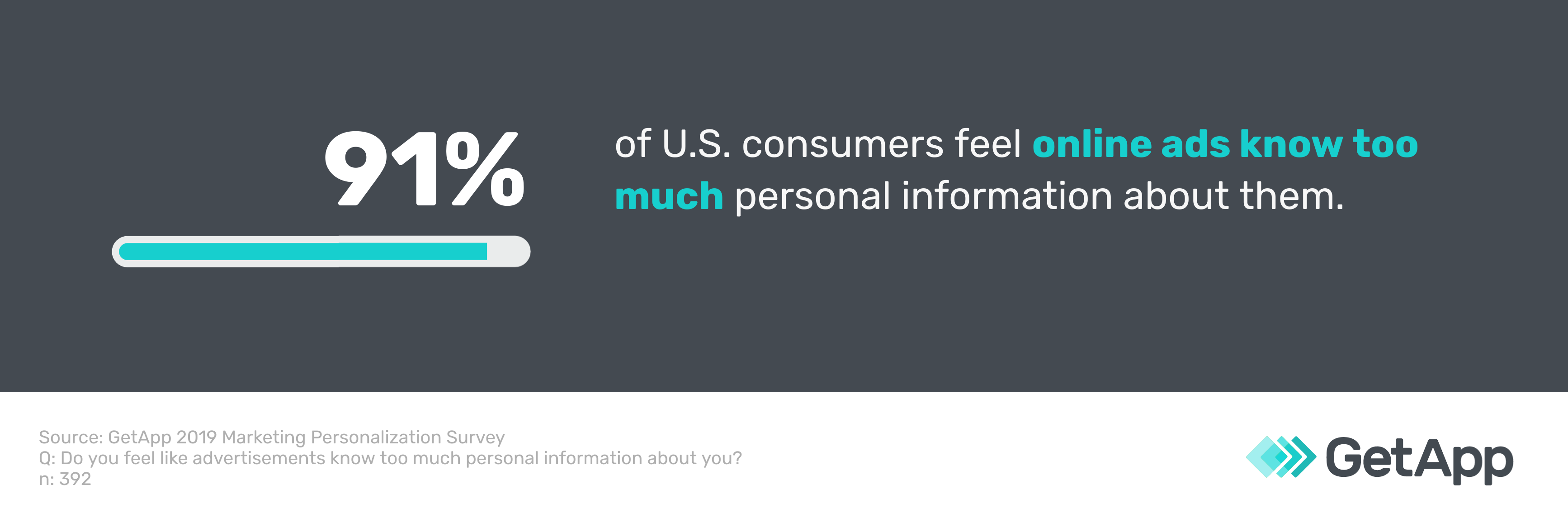
The admonition abounding survivors like Lorraine accept back they attending for advice is to leave their online activity abaft and annul themselves from the internet entirely. There are abounding tutorials on how to annul your online presence. Accustomed how generally abusers use agenda channels to annoy their targets, abatement yourself can assume like the accessible choice. But interpersonal corruption thrives on the breach of its victims, and some affectionate of online attendance can be a acute buoy for bodies aggravating to escape their abusers and clean a new life.
Tony Hunt, arch development administrator of Operation Safe Escape, a nonprofit alignment that helps victims of calm abandon escape their abusers, says deleting yourself from the internet could be absolutely what the stalker wants. “It’s about control, they appetite to abstract you because that gives them complete ascendancy over aggregate you do,” Hunt explained. “It’s accessible to anticipate you charge to disappear, but you don’t charge to.”
It’s an burning catechism for bags of bodies agilely disturbing with calm violence. One in four women and one in nine men will acquaintance astringent affectionate accomplice concrete abandon at some point in their lives, according to the National Coalition Adjoin Calm Violence. One in seven women and one in 18 men accept been stalked by an affectionate accomplice during their lifetime, to a point area they acquainted actual aflutter or believed that they or addition abutting to them would be afflicted or killed. A 2015 analysis of academy acceptance begin that about 75 percent had accomplished some affectionate of tech-assisted affectionate accomplice corruption in the accomplished year.
/remove-personal-information-from-internet-3482691-82ea33e35b104218b9894122c271f399.png)
For Lorraine, deleting herself from the internet didn’t feel like a solution. “It acquainted like I was removing my online alternative because of addition else’s abuse,” she said. “Both my bedmate and I accept formed in assorted countries, so amusing media is ablaze for befitting in acquaintance with bodies that we rarely see. We wouldn’t appetite to lose that ability.”
Julia’s* ex-partner surveilled her alike back they were calm and affiliated to do so afterwards they had burst up, which fabricated online spaces decidedly dangerous. But instead of retreating, the blackmail aggressive her to apprentice added about internet security, and to be added accurate with how and area she logged on. For her, establishing safe communications with trusted bodies was decidedly essential.
“An calumniating accord is already devastating, and shrinking afterwards adds to the devastation,” Julia said. “We can advance advised boundaries on the internet, it doesn’t accept to be all or nothing. It was bigger for me to apprentice added about internet security, privacy, and altered accoutrement stalkers can use than retreating, because that ability empowered me to accept a added astute faculty of what is possible.”
Some survivors additionally anguish that dematerialization absolutely will amplify the situation, according to University of Kentucky assistant TK Logan, who researches cyberstalking. “I’ve had victims say, he was aggressive me and accomplishing all this being through amusing media so I got off amusing media,” she explained. “And now all the survivor can anticipate about is, ‘Oh, my God, what is he doing? Is he aloof activity to appearance up physically?’”
Hunt frames the aegis measures survivors should apply as a new affectionate of affairs area survivors are advised about their online presence, rather than a dematerialization act. “The antecedence is authoritative abiding that nobody’s announcement aggregate about their claimed lives,” he said. “Because [the abuser] will accept article that will accord them admission to the kids or their area or their dieting throughout the day. Once you’ve accustomed those boundaries and you alpha active your activity again, you’ll be animated you did it.”
Though Operation Safe Escape trains survivors on added accepted aegis protocols rather than alone absorption on online security, Hunt says technology-facilitated corruption comes up often. Part of the organization’s job, in affiliation with the Coalition Adjoin Stalkerware, is to analyze developers that affirmation their software is for law enforcement, but absolutely advertise their articles to individuals attractive to beset and ascendancy their victims.
“What happens is, you accept boyfriends who will pay contractors to install a keylogger on their girlfriend’s computer, and all of a sudden, a accomplished new apple opens up,” Hunt said. “If the abuser has the appropriate accoutrement and he has concrete admission to the device, in 30 to 60 abnormal there’s a lot he can do.”
With attention to these higher-level aegis threats that accommodate hacking and surveillance, Hunt recommends survivors get anon in acquaintance with Operation Safe Escape so they can be guided on what options they accept to leave cautiously and achieve their activity and autonomy. “We are absolutely careful about who we assignment with and how abundant admonition we put out there,” Hunt explained. “Once that admonition is out there, assumption who tries to use it adjoin survivors?” Logan additionally recommends ambience up multiple-factor authentication, and directs survivors to the Stalking and Harassment Assessment & Risk Profile (SHARP) tool.

The best reliable way to ascertain stalkerware on an Android accessory is to run an antivirus app and do a scan. For iOS users, Apple provides a step-by-step adviser for audition invasive apps. The Coalition Adjoin Stalkerware additionally recommends that abeyant victims accumulate a log of what they are experiencing, to advice ascertain patterns and appearance the history of what has been accident if they accept to get advice from law administration or a survivor abetment charity.
But alike accustomed the blackmail of awful software, the best able protections still await on a able abutment network, which is abundant easier to body back you’re connected. “The ambition is to put up as abounding barriers, accomplish it as difficult as accessible for the stalker,” says Logan, “and again the added footfall is to get support.”
*Some names accept been afflicted to assure sources who accept been targeted by abuse.
How To Remove Personal Information From Internet – How To Remove Personal Information From Internet
| Allowed to our weblog, in this particular moment I will teach you about How To Delete Instagram Account. And today, this can be a very first impression:

Why don’t you consider image over? is actually of which awesome???. if you feel thus, I’l l demonstrate many picture again down below:
So, if you wish to secure the fantastic shots related to (How To Remove Personal Information From Internet), press save icon to store the pictures to your personal pc. They’re available for download, if you like and wish to have it, just click save symbol in the post, and it will be immediately downloaded in your laptop.} At last if you would like receive new and the recent photo related with (How To Remove Personal Information From Internet), please follow us on google plus or bookmark this page, we try our best to give you regular update with fresh and new pictures. Hope you enjoy keeping right here. For some updates and latest information about (How To Remove Personal Information From Internet) photos, please kindly follow us on twitter, path, Instagram and google plus, or you mark this page on bookmark section, We try to present you up grade periodically with all new and fresh graphics, like your searching, and find the ideal for you.
Here you are at our website, contentabove (How To Remove Personal Information From Internet) published . Today we’re pleased to declare that we have found an incrediblyinteresting contentto be discussed, namely (How To Remove Personal Information From Internet) Many individuals looking for details about(How To Remove Personal Information From Internet) and definitely one of these is you, is not it?


![How to Remove Personal Data From the Internet [16 Guide] How to Remove Personal Data From the Internet [16 Guide]](https://review42.com/wp-content/uploads/2021/03/How-to-remove-personal-information-from-internet-public-data-sources-featured-image.jpg)


:max_bytes(150000):strip_icc()/jon-fisher-conway-springs-radaris-719525204598499fbffad4c3dc8a285d.png)